General scheme of Today's Steganography
(KIT-STEGROUP)
<Steganography is ...>
If you have some secret data, you may encrypt it to make it unreadable for the third party. Data encryption is a solution to keep secret information unrevealed. It is based on a data scrambling using a secret key.
However, encrypted data will draw much more attention than non-encrypted data. The owner of the encrypted data will be suspected as he/she is hiding something. Therefore, encryption is not an almighty solution.
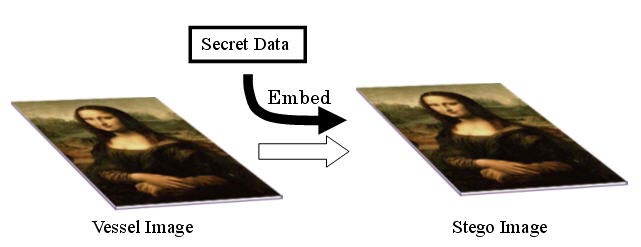
There is another solution which is called steganography. The general scheme of the today's steganography is as follows.
You will deal with two types of data in steganography. One is the secret data itself that is very valuable to you. The other is the media data that is called "vessel", "carrier", or "dummy" data. The vessel is essential, but not so much valuable. It is just a data in which the valuable data is "embedded" to hide. An "already embedded" vessel is called a "stego data." When you want to retrieve the embedded data, you can "extract" it from the stego data. For embedding and extracting you need a special program and a key.
A typical vessel is an image data with Red, Green, and Blue color components in a 24 bit-plane structure. The illustration below shows a general scheme of steganography in embedding.
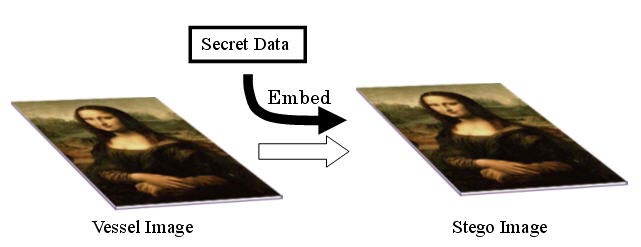
General scheme of steganography in embedding
Steganography is a very safe scheme because it hides both the content and the location of the secret information. There are many different methods to embed. It is practically impossible to detect which method is used for embedding. Steganography can co-operate with cryptography in the sense that it can embed "encrypted data" as well as non-encrypted one.
The most important point in steganography is that the stego data does not show any evidence to be suspected as "something is hidden there." In other words, the original vessel and the stego data must be very identical. A steganography user should discard the original vessel after embedding in order not to allow anyone to compare them.
One stego data must be re-usable as a vessel for another embedding. If not, such embedding scheme changes the structure of the vessel intrinsically. In other words, all vessel data must be repeatedly "re-usable." But only the "lastly-embed data" can be retrieved.
It is fundamental that the embedding capacity is large. The larger the better. For image steganography we are still confident that BPCS method is the best of all currently available steganography methods.
<File deception is ...>
"File deception" or "file camouflage" is a technique to hide secret data in a computer file which looks almost a steganography. But actually, it is a trick to disguise a secret-data-added file as a normal file. That can be possible because most file formats have some "don't-care portion." For example, a JPEG, MPEG3, or Word file allows any "extra data" be added to the file end. Even if such extra data are added, the JPEG, MPEG3, or Word files work just normally. Some people may misunderstand such a trick is a type of steganography.
However, such tricked files may have extra-lengthy file sizes, and they can be easily detected by most computer engineers. So, file deception is definitely different from steganography technique we are discussing here.
Many "steganography software" on the market today is based on the file deception. If you find a steganography program that increases the output size (i.e., the stego file size) just by the amount you have embedded, that program is obviously a file deception.
(Updated on June 13, 2019 by Eiji Kawaguchi)